A common disruption method used by cybersecurity attackers is a Distributed Denial of Service (DDoS). (Also see: Hacker releases source code of Mirai DDoS Trojan after targeting the IoT this weekend)
What makes the most recent example, referred to as the Mirai botnet, unique is that it did not rely on previously common techniques involving reflection and amplification methods to increase traffic to the target but were direct connection using spoofed address from the individual Internet of Things (IoT) devices themselves. Just by the sheer number of IoT device infections made it the largest DDoS attack recorded, says T.Roy, CEO, IoT Defense Inc.
 IoT Defense, Inc.’s Attack Threat Intelligence (ATI) backend observed the mass enumeration effort involved in the scanning of open and connected devices.
IoT Defense, Inc.’s Attack Threat Intelligence (ATI) backend observed the mass enumeration effort involved in the scanning of open and connected devices.
This effort is traditionally done to probe for vulnerable devices that could be candidates for infection and eventual botnet participation. The top five countries involved in the initial effort as recorded are listed in Table 1.
| Country | Unique Fingerprints | First Observation |
| China | 33,303 | 2016-06-05 15:09:50 |
| Vietnam | 12,094 | 2016-07-07 03:33:31 |
| Brazil | 9,018 | 2016-07-07 03:01:06 |
| South Korea | 7,242 | 2016-07-07 03:07:53 |
| Russia | 4,188 | 2016-07-07 06:08:48 |
Table 1: Top five (5) countries observed in the initial enumeration efforts
RATtrap offered its users dual protection by blocking the command and control virtual private systems (VPS) used for command and control after it was correlated in IoT Defense’s ATI datacenter via the RATtrap feedback loop. If command and control changed, RATtrap also enforced origin authenticity and would drop the spoofed requests.
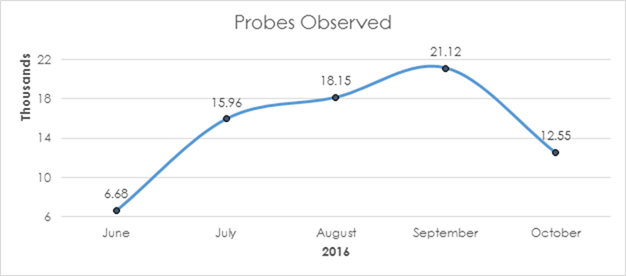
Scanning and discovery efforts have steadily increased month over month and show no signs of decreasing, as shown in Figure 1. Given the successfully execution of the recent DDoS attack and the release of source code for Mirai, we expect to see further usage of its capabilities and adaptation in the wild.
IoT Defense Inc. is a start-up company based in the Northern VA, USA. The IoT Defense team has multiple decades of cyber-security experience. Having focused on all forms of defensive and offensive security for enterprise and government, the team has come together to apply their collective insights to protect the consumer.
The teams mission is to build solutions, both hardware and software, to protect the consumer Internet of Things (IoT). RATtrap is the first step towards realising this goal.
The author of this blog is T.Roy, CEO, IoT Defense Inc
Comment on this article below or via Twitter: @IoTNow OR @jcIoTnow


