As IoT continues to mature and the volumes of connected IoT devices increase, the attention has turned to securing IoT. The larger number of devices have resulted in an expanded threat surface and greater opportunities for cybercrime. For OEMs and IoT solutions providers this presents two fundamental challenges: reducing crime and strengthening trust in IoT devices and the data they transmit.
Analyst firm Gartner reports that more than 80% of organisations have implemented some form of IoT and close to 20% have detected an IoT-based attack in the past three years. This demonstrates an ever-growing number of IoT enterprises feeling the negative effects of security breaches but there is still significant failure to put adequate IoT cyber security in place. The firm says fewer than one-third of chief information security officers are confident their information security can reliably assess and mitigate IoT risks. This will not help breed trust and confidence in IoT devices and data among users and customers.
Reducing crime and the opportunity to commit cybercrime are obvious priorities but being able to trust IoT devices, their identities and their data is the foundation of many IoT business cases and represents the future of IoT revenues. Only when data is trusted to come from a specific device and the security of the data itself can be assured can it be relied upon and used to feed the business need it serves. Fostering trust is therefore as important as preventing frauds and cybercrime to the success of IoT initiatives.
Importantly, IoT clouds are also under attack so threats are not just confined to device security. FireEye’s threat intelligence and incident response unit Mandiant has identified a flaw in a component of the Kalay cloud platform that can be exploited to hack systems. Many Kalay users are video surveillance devices and the vulnerability has the potential to allow attackers to intercept live audio and video data. This hack relies on accessing a Kalay user’s unique ID but it illustrates that IoT devices should not be seen as the only weak point and IoT cloud security will increasingly need to be addressed.
Regardless of where the attacks come, the reality is that they are increasing in frequency and systems designed to secure devices are themselves potential points of vulnerability. Cybersecurity specialist Kaspersky detected 1.5 billion attacks against IoT devices in the first half of 2021 via its network of honeypots which simulate a vulnerable device. This is twice as many attacks as the honeypot network recorded in the first half of 2020.
From cameras to combines, the attacks proliferate
Examples of IoT device security breaches range from surveillance cameras to combine harvesters. Last year, a group of hackers claimed to have breached a massive store of surveillance camera data collected by start-up Verkada. This allowed access to live feeds of 150,000 cameras inside hospitals, police departments, prisons and schools as well as at enterprises. Companies that had footage exposed included Tesla and Cloudflare and hackers said they had access to the full video archive of all Verkada customers.
These types of examples illustrate the need for IoT service providers and original equipment manufacturers (OEMs) to adopt a security by design approach that prioritises thinking about security at the design stage and sets out what mechanisms will be used and how these will be deployed and managed when large volumes of devices are in deployment. Of course, in lower-end IoT services this needs to be accommodated at very low cost so the cost of securing the device doesn’t outstrip the value of the service it provides.
Can IoT afford the cost of security?
Today there are 8.6 billion IoT connections, according to ABI Research. By 2026, that number will nearly triple to 23.6 billion and securing these will involve substantial investment. The firm says total revenue in the IoT security market will reach US$16.8 billion by 2026. That suggests that a typical IoT connected device could be generating revenue for security providers of 66 cents. For many types of deployment that additional cost will break the business case, while for others it will reflect tremendous value.
However, it may not be possible to extrapolate the numbers so simplistically. ABI Research says the amount of IoT security revenue does not always correlate with the amount of IoT connections, and some markets are expected to experience disproportional revenue as companies spend to address security.
The headline figure does illustrate a market in which there is willingness to devote sustained investment to security and that is encouraging. Even so, there’s a substantial hill to climb even with this level of projected investment. In addition, not every organisation is fully-aware or committed to securing their IoT devices – yet.
Kaspersky reports that, while two thirds of organisations (64%) globally use IoT solutions, 43% don’t protect them completely. This means that for some of their IoT projects, businesses don’t use any protection tools. The damage to customers, the brand and its reputation cannot be allowed to continue so greater investment is needed.
For OEMs and IoT service providers there are several important concerns, which Kaspersky has highlighted in Figure 1. It says 46% of businesses fear that cybersecurity products can affect the performance of IoT while 40% feel it can be too hard to find a suitable solution. There are also concerns about lack of skilled staff or specific IoT security expertise within the business, with 35% citing this as a top issue.
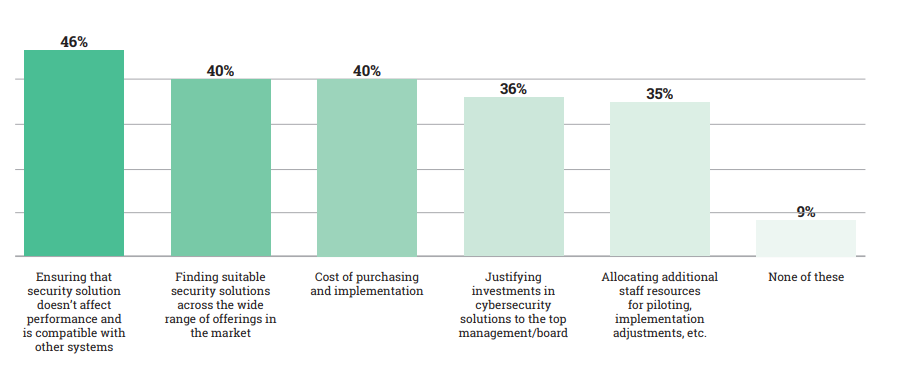
Source: Kaspersky
How to improve IoT cyber security
The wide array of attacks from distributed denial of service (DDoS) to malware and hacks on passwords creates a series of challenges for OEMs and IoT service providers to address on behalf of organisations that deploy IoT. In some cases, enterprises will try to address issues themselves but IoT service providers and OEMs are typically better-placed to secure IoT.
This is because they have experience of working across multiple types of devices, use cases, markets and jurisdictions so they are well aware of the correct techniques to use. They have both the IoT and security-specific skills needed, that are in short supply in the market. It will, for example, be hard for an enterprise to find the right people and the right structure to position their security stance effectively to protect their IoT operations.
The utilisation of cybersecurity is an important step but having the correct policies in place to support secure IoT is essential. Too many devices ship with default passwords or are subject users who change their password to something as simple as the word: “password.”
A large proportion of security breaches can be attributed to human error so efforts made by OEMs and IoT service providers to take matters out of users’ hands and embed security into IoT devices promise strong results.
The alternative is for enterprises to do it all themselves and invest in cybersecurity software, vulnerability management tools, password management software, network intrusion detection systems and so on. Each of these must be kept up-to-date, managed and maintained and adds a significant non-core list of tasks for an enterprise.
What can OEMs and IoT service providers do?
In addition to bringing their experience to customers they can assist by setting out how security by design can be achieved. Security by design is an approach to software and hardware development that moves security from being a bolted-on afterthought to a primary consideration undertaken at the design stage of an IoT device or service. Security by design will always outperform retrospective measures to addressing existing vulnerabilities and patches and is becoming essential in IoT as connected devices are readily addressable over the internet.
OEMs and IoT service providers can use their knowledge to assist customers to design security into their devices and ensure manufacturing itself is secure so authentication, for example, is protected. Other innovations are arriving to simplify key IoT security requirements and enable improved functionality.
The IoT SIM Applet For Secure End-to-End Communication (IoT SAFE) is a GSMA initiative that allows the SIM to be used as a hardware secure element or root of trust to achieve end-to-end, chip-to-cloud security for IoT products and services. It is widely accepted that the SIM or eSIM (embedded SIM) is ideally suited for this purpose because it offers the best protection against hacking, offers advanced security and cryptographic features and it is fully standardised.
Hardware tamper-resistant elements – with the hardware expressed as an integrated or embedded subscriber identity module (iSIM or SIM) that also contains a secure element – within the device are a standard technology that integrates the new GSMA IoT SAFE specifications. These help to deliver scalable security by design using well-known, proven SIM technology that is already in billions of devices and has been used for decades.
Hardware tamper resistant elements are important because they address the three key IoT security requirements:
- Mutual trust between the IoT device and cloud This end-to-end mutual authentication enables a TLS connection
- Protection of data at rest and in motion Data integrity Data confidentiality
- Scalability There are already billions of secure elements in the field
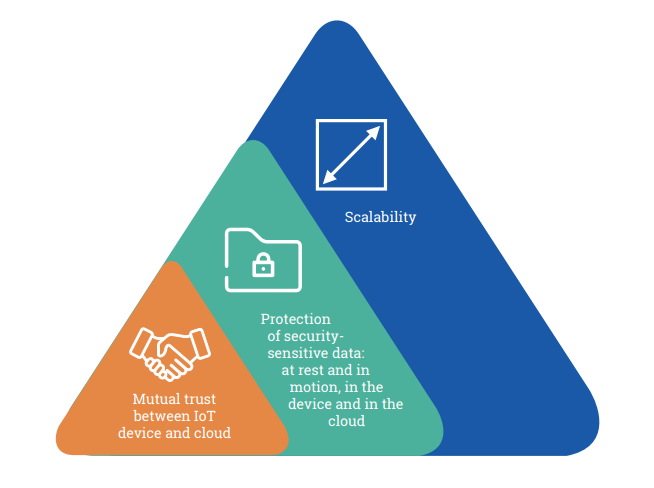
Source: Thales
The hardware tamper resistant elements then act as the root of trust and a cryptographic toolbox that stores private keys, digital certificates and security services. IoT SAFE deployment use the SIM or eSIM as a miniature crypto-safe inside the devices to establish a TLS session with a corresponding application cloud/ server. IoT SAFE provides a common application programme interface (API) for the highly secure SIM to be used as a hardware root of trust by IoT devices and is compatible with all SIM form factors.
The IoT SAFE applet runs on the SIM/eSIM OS and solves many of the challenges associated with IOT scalability because it enables the IoT device middleware to use the credentials and security in the SIM card for IoT. In essence, the secure element in the SIM/eSIM ties the device identity to the device and assures it as a source of data.
The use case of SIM, eSIM and more recently innovation in iSIM as a root of trust for end-to-end security for IoT products and services is compelling. In particular, eSIM and iSIM enable production, logistical and operational enhancements because there is no need for a physical plastic SIM and iSIM or eSIMs can simply bootstrap a localised connection at their point of deployment which means regionalised product variants are not needed. However, as a root of trust, the SIM becomes the enabler of a secure, trusted device that communicates data in support of whatever use case the enterprise requires.
Conclusion
SIM and eSIM vendors along with chipset manufacturers, cloud service providers and mobile operators have collaborated to develop the GSMA IoT SAFE standard and analyst firms such as Berg Insight expect the standard to gain significant traction this year.
The ability to take a security by design approach and install an IoT SAFE standard-compliant secure element into an IoT device at the point of manufacture addresses the requirement for both a root of trust and flexible connectivity within the device. Coming at the cost of the software for the secure element, the value proposition is attractive. OEMs and service providers are well-placed to roll-out IoT SAFE on behalf of customers with the possibility of creating IoT devices that have ‘security inside’ on behalf of their customers.
Comment on this article below or via Twitter: @IoTNow_OR @jcIoTnow